The problem of data breaches and cyber-attack is increasing rapidly with great online deals and 24/7 online updates. However, do you know what is the working behind when you browse the web? You might be using a Virtual Private Network with a proxy server at your organization or school.
Also, you can be a more tech person who is using a proxy at an individual level. A proxy server acts as a mediator between two parties and works as a protection wall from cyber-attacks and data breaching problems, and provides the user anonymity for online working.
Contents
What’s A Proxy Server?
A proxy server is an intermediate source between the internet and the user that separates the user’s original identity in online browsing. The proxy server provides you functionality, privacy, and security accordingly.
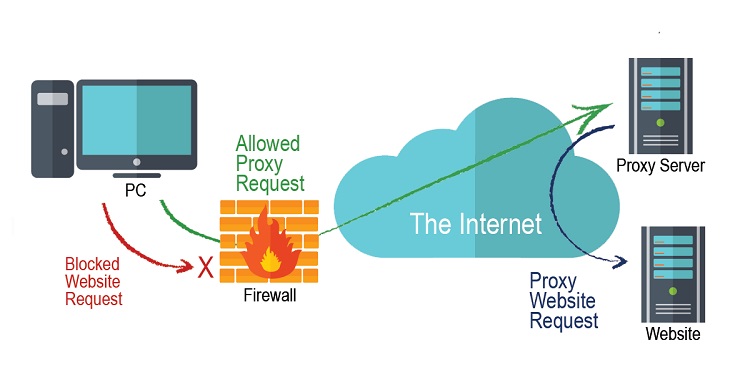
A proxy server works with a flow system like internet traffic will flow through a proxy server on the requested address. Therefore, the request comes from the proxy server and comes back to you from that requested website.
However, what is the need for a proxy server? The main reason is online data protection from cyber-attacks and data breaches. Modern proxy servers have additional features rather than forwarding web requests and enhanced network performance.
Proxy servers act as web filters and firewalls between the shared networks and provide security and speed up common requests. A good proxy server provides you with better protection from bad online stuff.
How Does A Proxy Server Work?
Each computer needs a unique Internet Protocol (IP) address, like a unique identification number. The post office knows the correct address to deliver the mails in the same manner the internet identifies its particular destination to forward the accurate information. All this process is regulated through the IP addresses.
Generally, a proxy server is a computer with the internet with an IP address that your computer already knows. Therefore, whenever you send a web request, that request goes to the webserver first, then gather the correct information according to your request and send back the response to the web page that you will see on your web browser.
Whenever the proxy server sends the web request further, it can also alter the data accordingly. However, you will get the required information. Also, it can alter your Internet Protocol address so that the webserver can’t detect the location of the user, and encrypt your data in an unreadable format and also restrict access to certain websites.
Why Should You Use a Proxy Server?
Various reasons that force users to use a proxy server at the organizational and personal level:
1. Control Internet Usage
Organizations and parents require proxy servers to control the internet usage of their employees and kids, respectively. Most of the companies restrict access to specific websites during working hours and monitor all your web requests, so they will know how much time did you spent browsing which site.
2. Bandwidth and Speed Improvement
Proxy servers provide better network performance and save all a copy of popular websites locally that can send you whenever asked. In such a way, it improves the speed and bandwidth of web proxy.
3. Benefits in Privacy
Several organizations, as well as individuals, use web proxies for the anonymous use of the internet. They can alter the IP address and other original information and forward or share it with others. Therefore, the destination server can’t detect the original information of the user.
4. Security Improvement
Proxy servers are good options for security purposes as you can encrypt your web requests and malware sites accessible through them. Several organizations use VPN with proxy servers for online security and privacy, such as controlling and verifying the access resources of the employees and securing connections to provide better online protection.
5. Access for Blocked Resources
Proxy servers provide access to restricted sites imposed by organizations and the government with anonymity. Proxy servers allow uncensored users to monitor restricted access to online websites.
Proxy Server Risks
There are possible risks associated with proxy servers. Therefore, we have listed some common risks that need to be cautious while selecting a web proxy:
1. Risks Are Associated With Free Web Proxies
Free proxy services are quite risky as they invest heavily in encryption or backend hardware. Also, free Proxy includes problems like performance issues, data security, and privacy, even stealing of personal information.
2. Browser History
Usually, a proxy server has users’ personal information, including original IP addresses and web requests that are saved locally in it. You have to be careful while using such proxies as they save your data and can use it against you. You have to take care of policies, including cooperation policies and law enforcement they follow.
3. No Encryption in the Proxy Server
You should not use a proxy that has no encryption because it simply means that forwarded web requests are simple texts not encrypted or anonymous. You have to use a reliable proxy server with an entire encryption package.
Types of Proxy Servers
Every proxy server works in different conditions and ways. Therefore, you have to select what properties you want from the proxy server and ensure that a particular proxy meets your expectation. Here are the types of proxy servers:
1. Transparent Proxy
A transparent proxy is easy to set up for the client as well as the server-side. It informs the website about the proxy server and pass-through the IP address, and recognizes you to the webserver. Transparent proxies are often used by businesses, schools, and various organizations for content filtering and other purposes.
2. Anonymous Proxy
The anonymous Proxy will not move through the Internet Protocol address to the website. Also, it will recognize itself as a proxy. Also, anonymous Proxy restricts marketing ads based on location, such as if the website CNN.com knows your location, they will surely target you according to that information. Therefore, these ad targeting techniques can prevent such websites; however, it is not guaranteed.
3. Distorting Proxy
A distorting proxy identifies itself as a proxy and allows a false Internet Protocol address to pass on. This Proxy will allow you to work anonymously. However, users can appear to be from a different location than the original for the restricted contents through passing the false IP address.
4. High Anonymity Proxy
High anonymity proxy servers make difficult the identification of traffic according to the persons. This web proxy changes the IP address periodically and protects it in the best way, such as the TOR network.
Conclusion
In some countries, Internet Service Providers (ISP) can control the bandwidth and internet traffic security of your network. Also, the ISP can inform users which sites can users can access or not. There is a large number of uncertainties present online.
Therefore, web proxy will help in some ISP restrictions. We hope this article will help you get proper information about the web proxy server details, including working and various types with functions!

